
MD5 vs SHA-256: Why MD5 Is Broken and How to Migrate
Learn why MD5 is cryptographically broken, how SHA-256 compares, and how to migrate from MD5 to SHA-256 in your applications. Includes practical code examples.

SHA-256 vs SHA-512: Which Hash Algorithm Should You Use?
Compare SHA-256 and SHA-512 in depth. Learn the differences in output size, speed, security, and when to use each algorithm for your project.
How to Verify File Integrity with Hash Checksums
Learn how to verify file integrity using hash checksums. Step-by-step guide for Windows, macOS, and Linux with MD5, SHA-256, and online tools.

Hashing vs Encryption: What's the Difference and When to Use Each
Understand the key differences between hashing and encryption. Learn when to use each, common algorithms, and avoid the mistakes that lead to security breaches.
MD5 vs SHA256 vs SHA512: Which Hash Algorithm Should You Use?
Compare MD5, SHA-256, and SHA-512 hash algorithms. Learn which is secure, which is broken, and which to use for passwords, file integrity, and security.
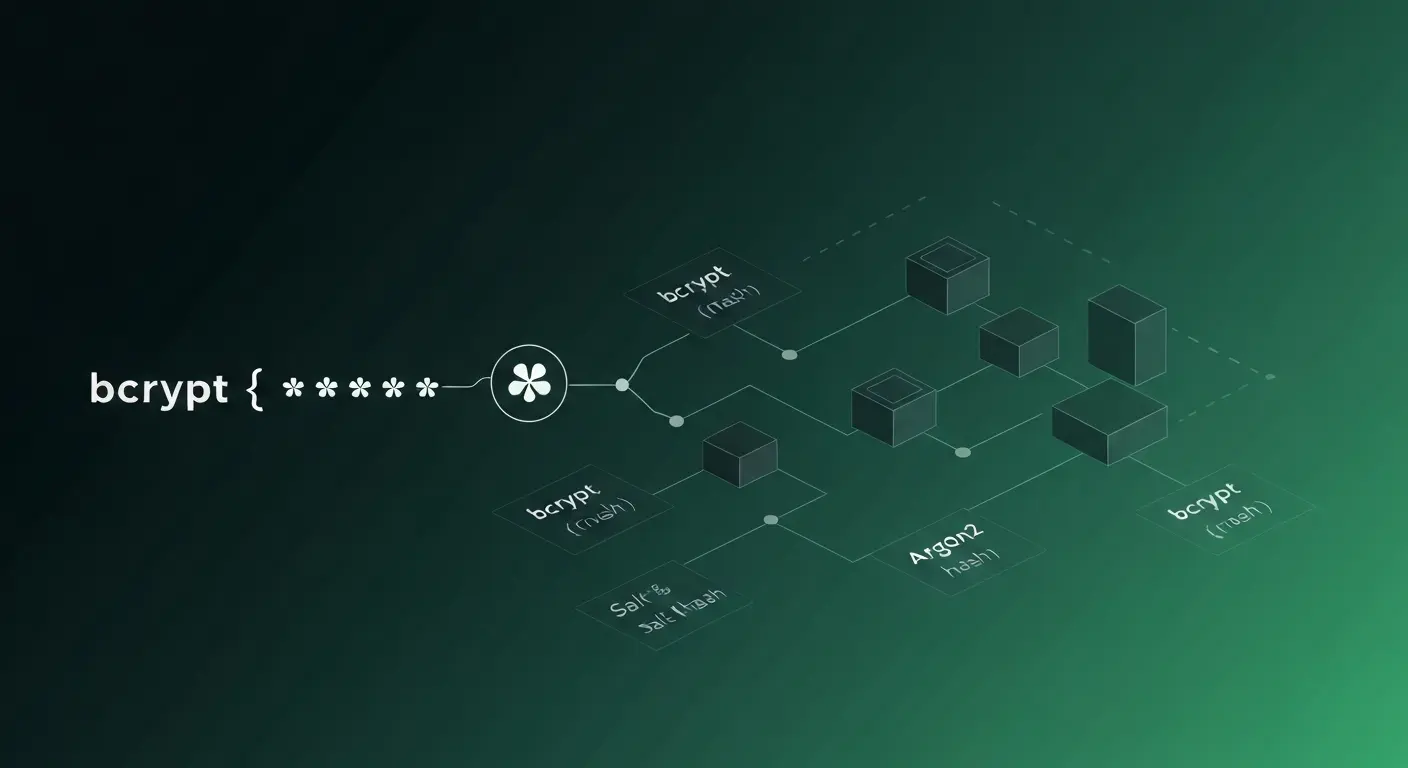
How to Store Passwords Securely: bcrypt, Argon2, and scrypt Explained
Learn how to hash passwords securely with bcrypt, Argon2, and scrypt. Understand why MD5 and SHA are wrong for passwords and implement secure storage.
What is SHA-256? The Hash Algorithm That Secures Bitcoin and the Internet
Learn how SHA-256 works, why it's secure, and where it's used -- from Bitcoin mining to TLS certificates. Complete guide to the world's most important hash algorithm.
Need to Generate a Hash?
Generate MD5, SHA-256, SHA-512, and more hash values instantly — 100% client-side, no data sent to servers.
Open Hash Generator